How adam:ONE® Works
The world's first Zero Trust Resolver - the first practical and scalable implementation of Default-Deny-All networking
The Core Philosophy
A fundamental shift in how network security works
Traditional Approach
"Trust by default, deny threats"
- Allows all connections by default
- Relies on detection to block threats
- Attackers exploit the gap before detection
adam:ONE® Approach
"Deny by default, trust verified connections"
- Blocks all connections by default
- Only allows DNS-verified/policy-allowed connections
- Disrupt the attack chain without the need to detect
Key Technologies
Six pillars of the adam:ONE® architecture working together to deliver true Zero Trust
Muscle-Brain Architecture
Distributed "muscle" nodes deployed on-premise or in-cloud handle local traffic decisions with resilience and performance. Centralized "brain" controller provides orchestration and policy management.
- Local traffic processing for speed
- Centralized control and visibility
- Resilient if controller goes offline
Don't Talk To Strangers (DTTS)®
Patented technology that enforces DNS as the root of trust. Denies all IP connections by default unless first verified by DNS and allowed by policy, or explicitly permitted via configurable Enablers. Provides dynamic egress control that prevents circumvention, breaks C2 connections, and eliminates data exfiltration channels.
- DNS becomes security checkpoint
- Blocks direct IP connections
- Breaks C2 and prevents exfiltration
AI-Driven Dynamic Allowlisting
adam:ONE® utilizes AI/ML engines to power dynamic allowlisting. This overcomes the issue of maintaining a static allow list and enables a "Never trust, always verify" zero trust approach without disrupting business operations.
- Fixed Rules, AdaptiveAI, ReflexAI
- Policy matched to user or device role
- See detailed breakdown below
DNSharmony® Aggregation
Aggregates multiple pDNS threat intelligence sources including open source feeds (Cloudflare, Quad9, CleanBrowsing, AdGuard) and commercial services. Provides pDNS redundancy, continuous domain validation, and acts as resolver of last resort with real-time threat intelligence.
- Multi-source threat intelligence
- Redundant pDNS resolution
- Enhanced detection accuracy
Full Layer 2 Visibility
Complete network visibility with automatic device discovery and inventory. Enables automatic quarantine and per-network policy assignment - the value of NAC without the complexity.
- Real-time device inventory & automatic quarantine
- Complete East-West traffic protection
- Automatic shadow IT detection
Sovereign Data Custody
Privacy by design: honors TLS and end-to-end encryption without proxies. No centralized decryption required. Sovereign data custody with distributed protection.
- No TLS interception needed
- End-to-end encryption preserved
- Decentralized architecture
Intelligent Policy Engines
adam:ONE® utilizes AI/ML engines to power dynamic allowlisting. This overcomes the issue of maintaining a static allow list and enables a "Never trust, always verify" zero trust approach without disrupting business operations. Policies are assigned per device or group, enabling granular control down to the individual device to address a non-uniform attack surface.

AdaptiveAI™
Takes a learning mode approach over 30 to 90 days on a per site or per network basis and dynamically adds domains as requested by user(s). Each request passes through a cloud-based sandbox testing and AI inspection which deems whether it is safe. Only domains deemed safe from all discovered dependencies are added to the dynamic allowlist.
Recommended for:
- - Very defined user roles (e.g. Accounting)
- - High Value Assets such as C-suite
- - Incident Response (skip learning phase)
- Phishing mitigated - only allowed domains can connect
- Midstream redirect attacks blocked by default
- Domains held for human inspection before allowing

ReflexAI™
Patent pending dynamic allow-listing engine where 82 domain categories/tags are sorted into 5 decision buckets: Always Block, Block, Review, Allow, Always Allow. The AI/ML engine handles conflict resolution with 3 decision levels: Permissive, Hold for Human, Protective. No learning mode required - dynamic allow-lists are created in real-time with an average 20ms response time. That is 20 decisions per blink of an eye, with no disruption to the end user.
5 Decision Buckets:
- User-transparent protection - no disruption
- Proactive defense against phishing and redirects
- Uncategorized/unknown domains denied by default
- Appropriate Use Policies enforceable
Composite Static Rules
Using pre-made lists or by observation, a collection of required internet domains and/or FQDNs are established as an allow-list. Fixed traffic to only allowed resources with no circumvention even if the asset is compromised.
Typically used for:
- - Active Directory Controllers
- - File/Application Servers
- - Web Servers
- - IoT Devices, Printers/Scanners
- Fixed domain traffic to only allowed resources
- No circumvention even if asset is compromised
Combining any of these policy engines with DTTS® brings devices into a Zero Trust Connectivity (ZTc) state - proactively protected with true egress control against malicious outbound connections such as C2 beacons or data exfiltration. Even if a user clicks a malicious link, the Default-Deny-All state will refuse the connection unless verified and allowed by policy.
The Protection Flow
How adam:ONE® processes every connection request
Start in Default-Deny-All State
Every device begins with zero network access. Using aggregated pDNS intelligence merged with AI-driven dynamic allowlisting (AdaptiveAI or ReflexAI), a policy is built as the device needs to access verified connections to web services.
DNS as Root of Trust
Don't Talk To Strangers (DTTS)® technology enforces DNS as a functional root of trust, denying all IP connections by default unless first requested by DNS and allowed by the dynamic policy. This prevents direct IP-based attacks.
Verify and Open Connection
If allowed by policy, adam:ONE® opens a hole to establish the verified connection. The connection is monitored in real-time and collapsed as soon as it expires or is no longer needed.
Cross-Check with DNSharmony®
Allowed connections are continuously validated by DNSharmony® aggregation of pDNS resolvers of your choice. When used with AdaptiveAI/ReflexAI dynamic allowlisting, DNSharmony acts as a resolver of last resort - providing a final check to ensure a trusted domain hasn't gone "bad" while aggregating threat intelligence in real-time for resilience beyond a single resolver.
The Result
Zero Trust connectivity for any device requesting connection through adam:ONE®. ZT protection invisible to the user.
Where adam:ONE® Lives in Your Stack
adam:ONE® integrates seamlessly with your existing security infrastructure, working alongside your current tools while providing foundational Zero Trust protection at the DNS layer.
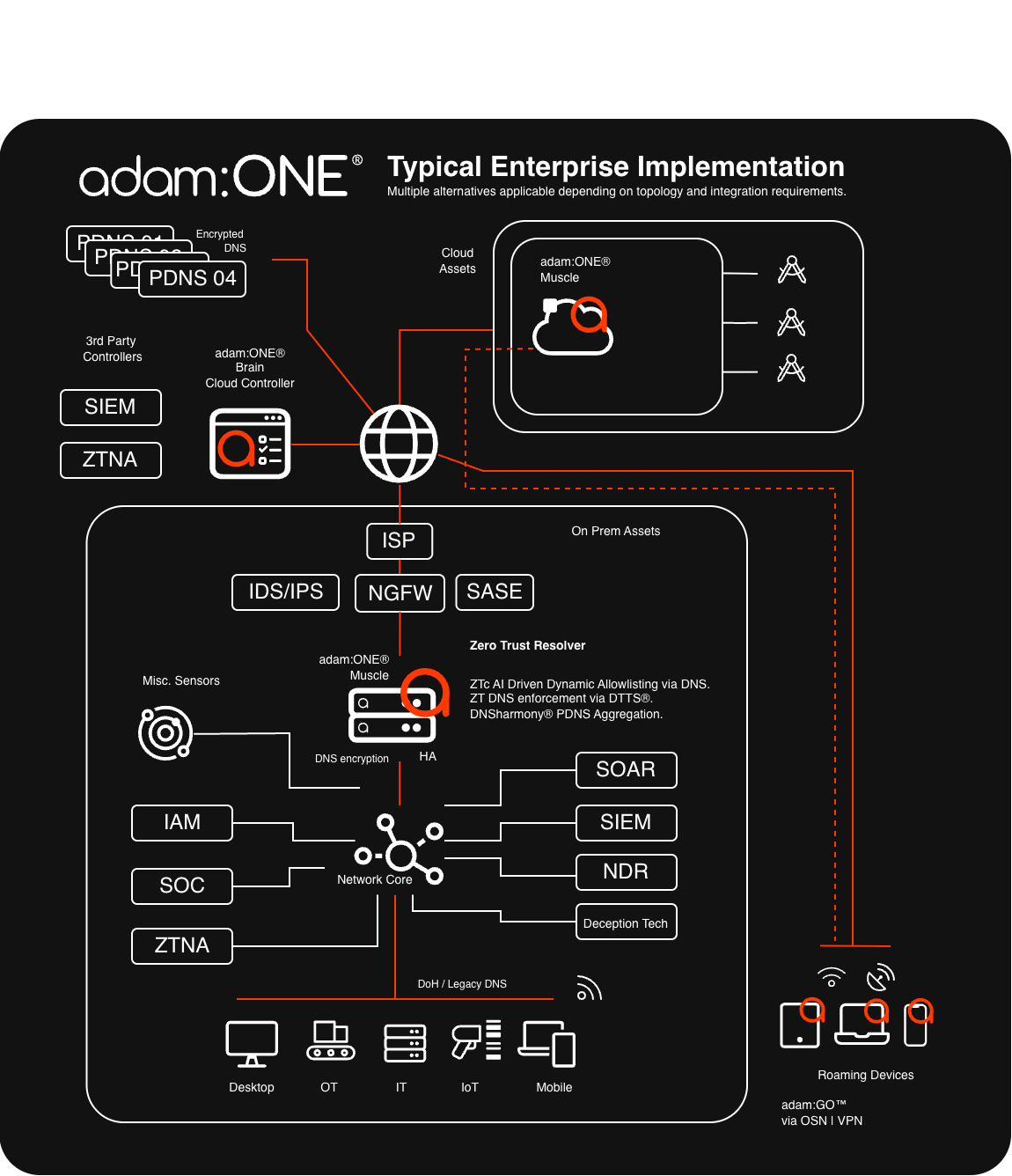
Complements Existing Tools
Works alongside SIEM, SOAR, NDR, IDS/IPS, NGFW, and ZTNA solutions
Zero Trust Resolver
AI-driven dynamic allowlisting via DNS with DTTS® enforcement and DNSharmony® aggregation
Flexible Deployment
Supports cloud assets, on-prem infrastructure, and roaming devices via adam:GO®
Device-Agnostic Protection
Out-of-band protection means adam:ONE® works with all types of devices including OT, IoT, and IT with no endpoint agent required
IT Devices
Laptops, desktops, servers, mobile
IoT/IIoT/MIoT
Smart devices, sensors
OT/ICS
Industrial controls, SCADA
Legacy Systems
Any OS, unmanaged devices
Proven in Critical Incidents
These technologies come together powerfully in incident response scenarios. adam:ONE® has been deployed as a first and critical tool for IR, enabling organizations to immediately adopt a ZTc state, neutralize active threats and restore operations within hours while maintaining complete radio silence to threat actors.
See Real-World Case Study